
Attack Modeling a Forgotten Password System
This Attack Model maps potential attack vectors in a typical forgotten password …
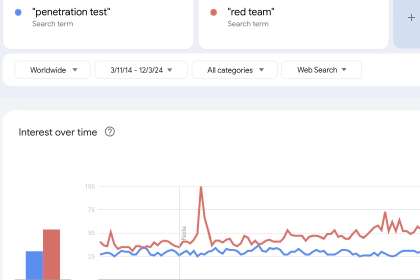
Pentesting now seems like a dirty word.
This struck me when I was reading Open AI’s recent post “Advancing red teaming …

There is one area of information security that is conspicuously absent from ATT&CK.
If your tooling only applies the …

At it’s core, an Attack Library is a list of all possible attacks against a component of your design. We use it almost …

Everyone? I’m not so sure…
Imagine the early 2000s… Britney Spears is playing on the radio, the …

This Attack Model maps potential attack vectors in a typical forgotten password system. The goal is to catalogue …

STRIDE has not aged well…
I’ve seen first-hand the thick PDFs and Excel files that my clients have had delivered …

A few years ago I was brought in to help with security for a project at a large retailer in the UK. They were building …