
Who Is Responsible for Security?
Everyone? I’m not so sure… Imagine the early 2000s… Britney Spears is playing on …
Let me tell you a story…
A few years ago, I was working with a company that had a traditional approach to security. You know the type: a big firewall around the internal network, with the assumption that everything inside was safe and cozy. As long as you were “in the network,” you were trusted. They had one big Active Directory (AD) domain and everything could access everything else.
That assumption came back to bite them. I was hired to do a pentest of some new APIs and I realised quickly that they were themselves talking to some other, older APIs that had been running the company’s core business for the past 20 years. Since I was inside the trust boundary, I could access the old APIs directly and bypass the authentication and authorisation enforced by the new APIs.
Those old APIs were COBOL - which may give away that we’re talking about a bank - and I was able to use Cross-Site Request Forgery (CSRF) to have any of their customers transfer all funds out of their account and in to my account. That was the wake up call they needed.
Fast forward to today, where everyone is remote, apps live in the cloud, and every device has WiFi, it’s impossible to rely on the idea of a trusted internal network like that bank did. This is where Zero Trust comes in, and it’s been a game changer.
Today’s networks are borderless. I mostly work from home (for now, ha), my coworkers are scattered across the globe, and everyone is accessing company apps on personal devices. This isn’t just a temporary thing; it’s the way work happens now. So, trying to create a trusted internal network is like putting up a fence around an empty field. The real action - and exploitation - is happening elsewhere.
One of the big shifts we’ve all had to embrace is that it’s not about the network anymore; it’s about identity. Every time I want to access company resources, whether I’m on my phone, laptop, or some other device, I have to prove who I am. I log in through an Identity Provider (IdP), which makes sure I’m actually me.
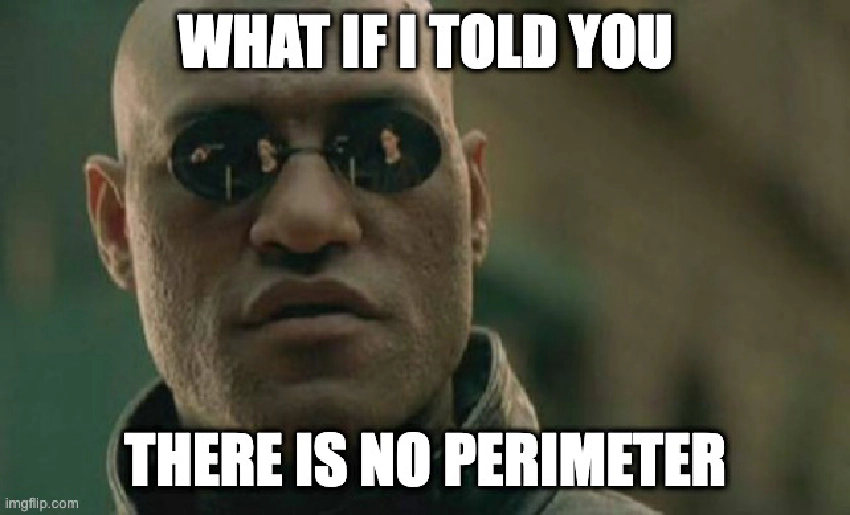
There has been much hoo-ha about Identity being the new perimeter, but I don’t think that’s accurate. I don’t think there is a perimeter at all.
Zero Trust flips the old security model on its head. Instead of assuming that everything inside the network is safe, it assumes nothing is safe no matter where it’s coming from. The idea is simple: never trust, always verify. It doesn’t matter if you’re sitting at a desk in the office or working from a café in Changi Airport, you have to prove who you are every time.
Zero Trust also means there’s no such thing as a free pass after login. Just because I’ve authenticated doesn’t mean I’m off the hook. Every single request to perform a restricted action has to be authenticated. That’s usually with an OAuth token or a session ID, which have become the new targets in red team exercises to get around MFA.
In the end, Zero Trust has changed the way I think about security. Instead of hunting for unpatched servers in external attack surface, it’s now the norm for offsec folks to go phishing for identities instead.