
Attack Modeling a Forgotten Password System
This Attack Model maps potential attack vectors in a typical forgotten password …
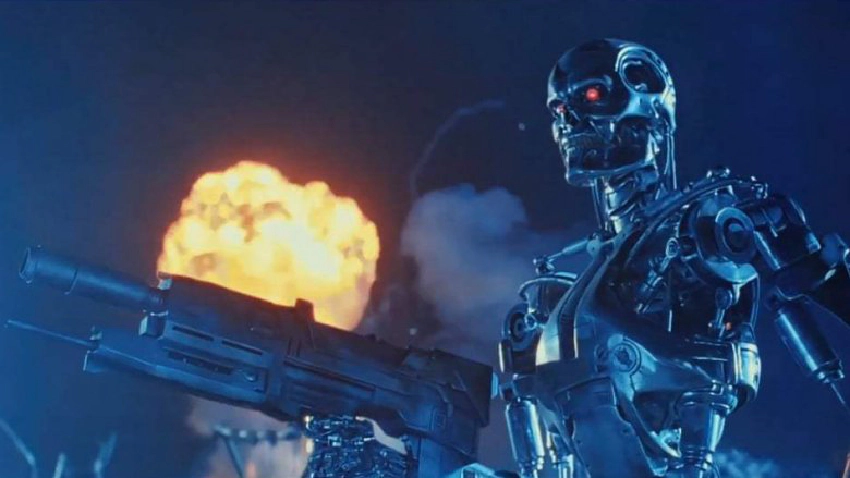
The opening scene from Terminator 2 takes place on July 11, 2029. It’s eerily close to when I expect several Attack-focused AIs to be operational and effective (maybe even earlier?).
They lived only to face a new nightmare, the war against the Machines…
Bug bounty and pentest vendors are currently training AI models using all of the exploitation tricks sent through them. We can assume nation states and organised crime are doing the same thing. Their capability will come down to the efficacy of the models and the quality of data used to train them.
My opinion is that bug bounty vendors will have an edge here, and be able to offer both an AI Attack product and an AI Defence product. The sheer numbers and diversity of talent enrolled in bug bounty programs likely surpasses most individual pentest vendors and nation states. Of course, existing XDR and network products are also training, but they will find it much harder to sort the wheat from the chaff. They have a lot of normal data to go through before finding and labeling the attacks.
Thankfully Terminator 2 got one thing wrong: it won’t be us fighting the machines, it’ll be our own labeled, trained-with-attacks AI Defence.